How do I know that my PHP or Apache version is vulnerable?
You can find vulnerabilities for the particular version on CVE details. You should use the lastest versions of server components, currently:
- Apache 2.4.39 (major version 2.2 is out of suport now)
- Nginx 1.16 (stable) or 1.17 (mainline)
- PHP 7.3.6 or 7.2.19
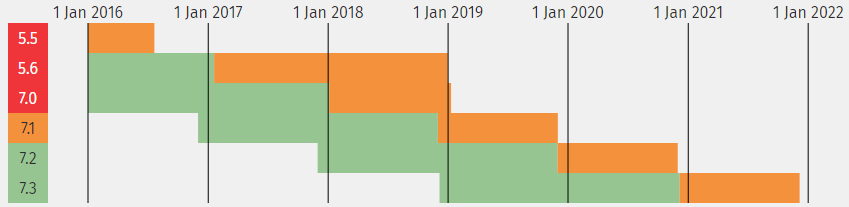
Also keep in mind, that every PHP major versions is fully supported only 2 years. For example PHP 7.1 is at the end of its life and the security support will end in 5 months.
You were talking about the security headers, which one can I use?
There are plenty HTTP security headers, you can use some of them pretty easily:
- X-XSS-Protection – tune browser’s XSS auditor behavior, we want to block the page if any problem is detected
- X-Frame-Options – can block loading the page in frame – prevents clickjacking
- X-Content-Type-Options – can disable content type sniffing
- Strict-Transport-Security – forces to use HTTPS everywhere
You can find the .htaccess rules here.
Another useful header is Content-Security-Policy, but it could be very tricky to deploy, especially if you use Google Tag Manager or a similar tool. It allows you to control your resources origins in detail, but you must specify all of them. The new version 3 provides a new feature strict-dynamic to load other resources from a trusted script, but the support in browsers is limited. There are some tricks how to prepare compatible rules.
Referrer Policy header could be also useful.
It seems, the storing DB password in the wp-config isn’t a good idea as well as store it in the environment variables. How to do it properly?
It isn’t bad idea, it is pretty normal approach. But for a better DB credentials protection you can use really long password and split it between wp-config and environment variable. The best solution is to use the secret store like HashiCorp Vault.
How to block user names harvesting?
You can block the URL queries trying to do it. It is a simple .htaccess rule and if you use Nginx you can get inspired from our Nginx configuration.
In case of REST API, you can block access to API for the anonymous users (e.g. with Disable REST API plugin), or you can filter out any sensitive information with my mu-plugin Enhancer.
What about the e-mails leaks? Is it a real problem?
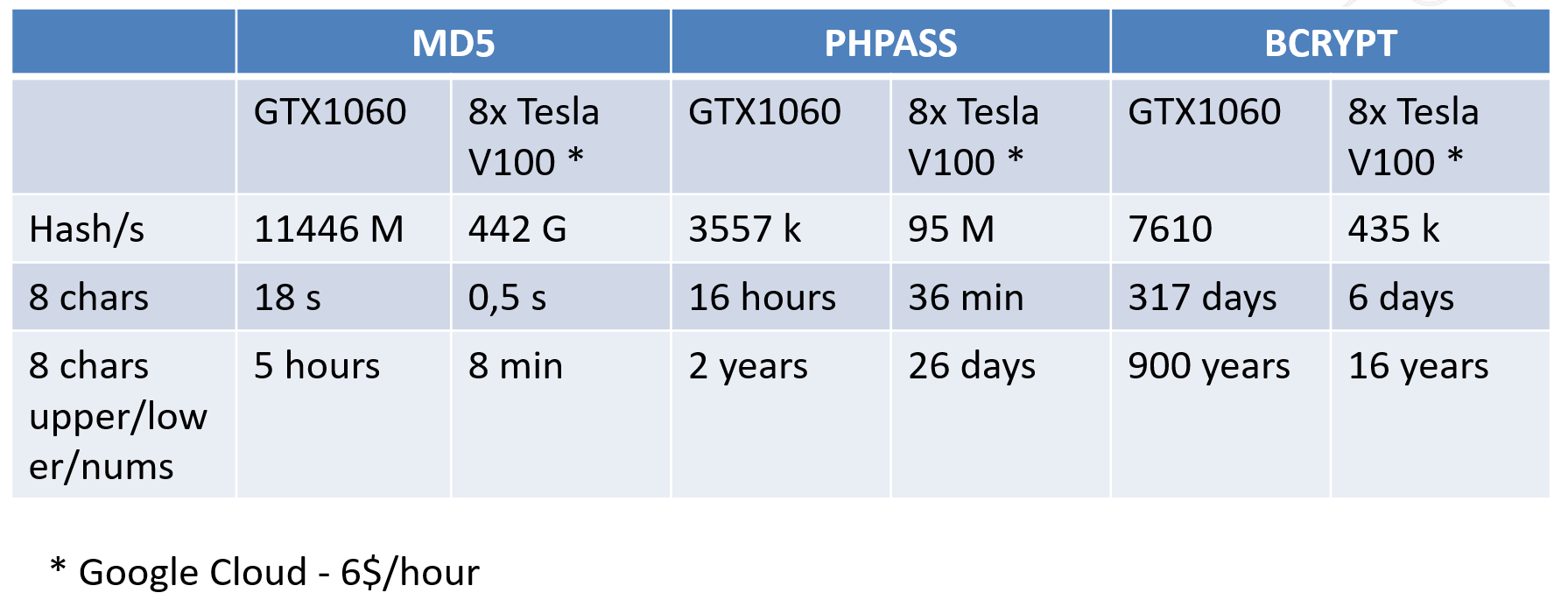
I think it is, especially in case of comments and in the age of GDPR. Cracking MD5 is pretty fast, and the most of e-mails have a simple format – usually contain few lower case chars, maybe one dot + @ + your domain/gmail.com/hotmail.com etc.
One way how to make harvesting a little bit complicated is to filter sensitive information out of REST API (again the same mu-plugin – just uncomment the line with rest_prepare_comment filter).
But the root cause are the Gravatars. The hashes will be still available in comments, however at least they will not all be in one place.
The easiest solution is to disable Gravatars completly in the comments setttings, or replace them with something different. I made a very simple plugin which replaces the Gravatars with generated SVG, so it is still possible to recognize individual comenteers.
How to defend against password leaks?
Prevention is the best way. You should use uniqe passwords generated from the password manager and multifactor authentication if available.
Another layer of prevention is on the application side – you should use bcrypt to hash the passwords. It reduces the impact of possible DB leaks. To enable bcrypt you can use my mu-plugin again (you need to reset all passwords to use a new hash).
It would be great to detect the leak. One simple trick is to create a fake user with a unique email, which you don’t use anywhere, and with a unique simple password of google zero return phrase.
If you start receiving spam on that mail, there was a leak. You can also register the mail to the Have I been Pwned? and setup Google Alert to your unique simple password.
Can you recommend a password manager?
There are some well known brands. I recommend to try few of them and then select the most comfortable one. Comfort is priority number one if you want to use it regularly. Most password managers have both a mobile app and cloud syncing, so you can use it everywhere.
- LastPass – I use this one, it is free for the personal use on multiple devices
- 1Password
- Dashlane
- Bitwarden – opensource, you can run it on-premise
- EnPass – use your own cloud storage (Dropbox, Google Drive,…), one time purchase
- KeePass – offline, I use it for SSH keys and other non-web secrets
What about 2FA?
Just start to use it! 🙂 The proper setup can make your life much easier. I recommend you to use HW keys (e.g. from Yubico), a mobile authentificator as a backup and backup keys stored in the password manager or in printed form in a tresor for case of the apocalypse.
The Yubico blue ones are ok, but I can’t imagine my life without the Nano ones.

On WP side you can use this small plugin called Two-Factor.
Should I use Google Authenticator or a different one?
Even if the application says that it supports only Google Authenticator, you can use any TOTP application.
A good example is LastPass Auhtenticator or Authy – the main benefit is they sync your tokens, so when you replace your phone, you don’t start from scratch.
There was a “Black Market price list” in your presentation. Why are some prices so different?
The prices on the Black Market are based on the risk/usability market law.
A hacked WP site costs only around 1$, because it was probably hacked through a known vulnerability, therefore it will be “rehacked” very soon.
An interesting thing is the price of a hacked e-mail account, which costs usually around 1$. It is because the most of mails are hosted by big providers like Google or Microsoft with a really good compromise detection, so if you try to login from a strange location, they will block you. That’s why having credentials to this mailboxes is pretty useless…
Booking or AirBnB accounts are sold for a little bit higher price – it is because the bad guys will know that you aren’t at home and they can rob you, or use your house to delivery goods paid by your stolen credit cards. With your hacked Netflix account, they are able to stream copyrighted content to the countries where it is not legally available.
High price is offered for a PayPal account paired with a card. It is because PayPal didn’t use 2FA for a long time. So, there is really good chance to abuse it.
Any details about your GIT scan?
Sure, you can read all about it here.
So, you are saying it is not worth to hide the WordPress version?
There are many ways to detect WP version. If you want to do it right it would be hard work and the effort doesn’t worth the results you get.
The key is to keep your WordPress (or any other opensource) up to date. There are tools which can be very helpful for this task, for example MainWP for central management.
If you are interested in the topic, I published an article about hiding WP version.
What about changing the administration URL?
The main point here is to prevent bad bots guessing the passwords. Hidden/limited login = no requests from bots = no resource consuming.
If you agree with me and this is the main reason to hide backend, I think that limiting the access to wp-login.php is suffiecient. You can limit the access to this file to a set of allowed IP addresses/VPN or only to your country.
You can also try my small Custom Login mu-plugin – it allows you to “register” your own login URL and you have to visit it earlier than wp-login.php.
If you want to change the URL address completely, you should keep in mind that various compatibility issues may arise.
I never hear you can use PHPmyAdmin as a backdoor.
It is one common issue of all DB management tools. There is a special function allowing you to load the content of a file into the database table. You must be the root user to do it, but it can be easily achievable – just connect to your own DB server, where you have the root rights. You will be able to read any accessible file from the server where PHPmyAdmin is running with LOAD DATA LOCAL INFILE.
More info:
- https://www.phpmyadmin.net/security/PMASA-2019-1/
- https://medium.com/bugbountywriteup/adminer-script-results-to-pwning-server-private-bug-bounty-program-fe6d8a43fe6f
NEVER leave any debugging/management scripts in the production!!!
Do you use any security plugin?
No, we implemented almost all funcions of security plugins on the server side, so they aren’t necessary for us. However, I recommend to use them in general. There are some interesting plugins, which totally differ in their philosophy:
- WordFence – all happens on your server, they have a good login protection, great malware scanning features and fine firewall. Also a paid version with more features (much recent firewall rules, country blocking and shared database of attacking IP addresses) is available.
- Sucuri – paid service, you direct all traffic to their service, they filter out the malicious requests and send the clean traffic to your site.
- MalCare – relatively new plugin, the main idea is to sync all your data to their service and make all cleaning there, so the malware scan don’t burn your server. It is basically an intelligent back up solution. They also provide a nice login protection and decent firewall blocking the most common attacks.





Leave a reply to jonas02 Cancel reply